Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Active information gathering is the foundation for the network mapping step. As we discussed in the active information gathering post, NMAP is one of the common swiss-amry knife tools for network-based information gathering.
When an attacker collects enough information about the target, then they have an opportunity to create a network mapping of the target network.
https://cyberenum.com/2021/07/nine-steps-in-hacking/
In this post, we give detailed information about NMAP because it is pretty common for network data discovery, a stable, community-supported tool. This post is like a long and detail guide line for beginer’s in the cybersecurity field. We how you enjoy and test our explanations.
Nmap (“Network Mapper”) is a free and open-source utility for network discovery and security auditing. Nmap uses raw IP packets in novel ways to determine what hosts are available on the network, what services (application name and version) those hosts are offering, what operating systems (and OS versions) they are running, what type of packet filters/firewalls are in use, and dozens of other characteristics. It was designed to rapidly scan large networks, but works fine against single hosts. Nmap runs on all major computer operating systems, and official binary packages are available for Linux, Windows, and Mac OS X.
For details visit nmap.org
syntax: nmap -sP <target>
nmap -sn <target>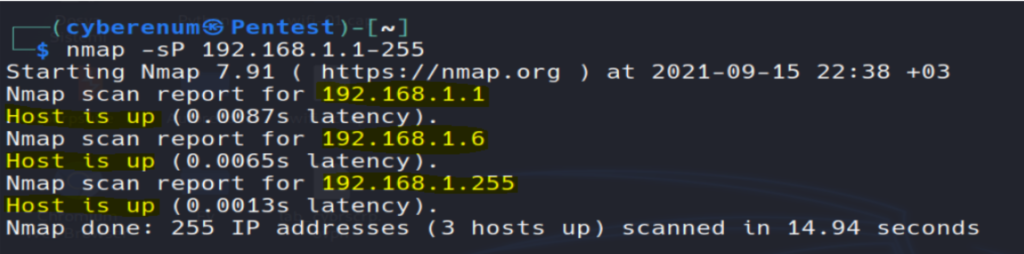
How it Works
Nmap uses the “ -sP / -sn “ flag for host scan and broadcasts ARP request packet to identify IP allocated to the particular host machine. It will broadcast ARP requests for a particular IP in that network which can be part of the IP range 192.168.1.1-225 is used to indicate that we want to scan all the 256 IPs in our network. After the active host will unicast the ARP packet by sending its MAC address as a reply which gives a message Host is up.
Aim: To identify a port is open or closed.
Port Status: open, clode ( no application listening on the port ), filtered ( the probes were not received and state could not be established, also indicates that probes are being dropped by some kind of filtering ), unfiltered ( the probes were received but a state could not be established ), open/filtered ( the port was filtered or open but Nmap couldn’t establish the state ), closed/filtered ( he port was filtered or closed but Nmap couldn’t establish the state
syntax: nmap -p [port#] <target>
nmap -sT [port#] <target>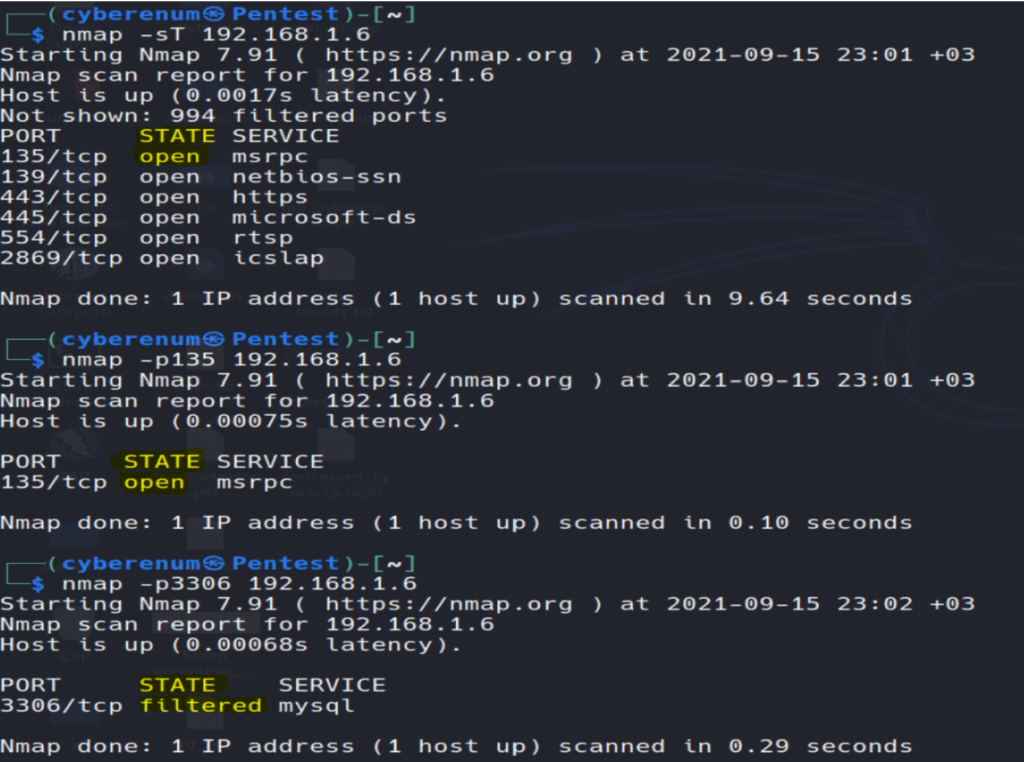
How it Works
Nmap uses the argument -p for defining the port range to be scanned. This flag can be combined with any scanning method. In the above example, we used the argument –p135 to indicate to Nmap that we are only interested in port 135. Can be written as nmap -p135,139 192.168.1.6 and nmap -p1-1000 192.168.1.6 also we can scan all open ports nmap -p1-65535 192.168.1.6 –open.

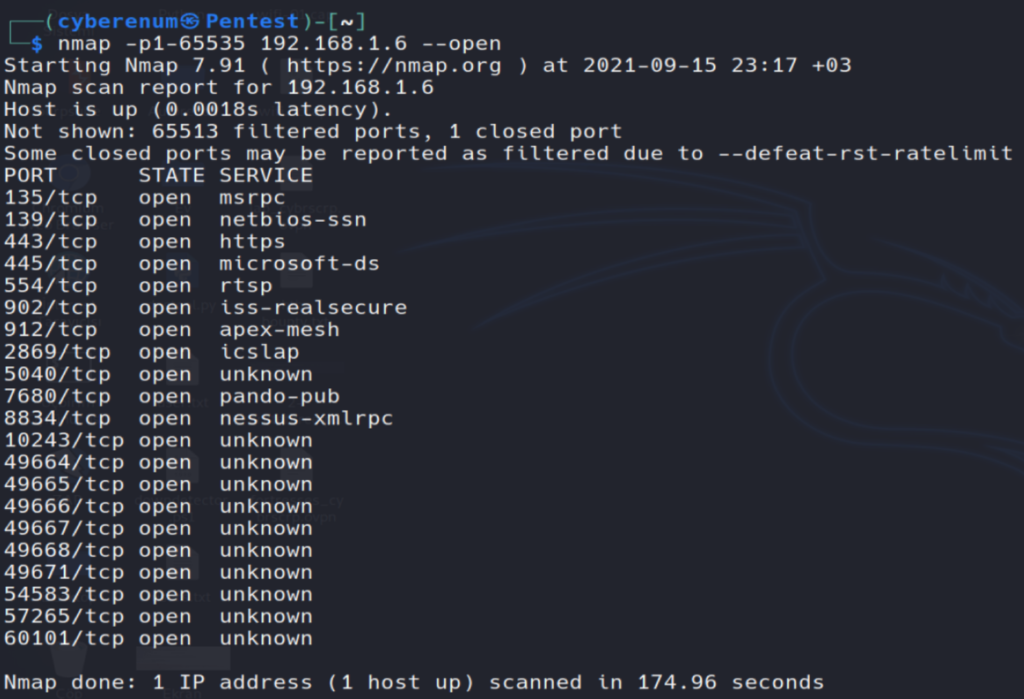
In addition to port range, all ports scan, we can scan specific ports by protocol and port service name attributes. By default, port scan prefer to enumerate the state of TCP ports but if you want to scan TCP port as well as UDP port then execute the following command given below:
syntax: nmap -pT:25,U:53 <target>Similarly, we can use -p option for port service name scans. If you don’t know the accurate port number for enumeration then you can also mention the service name for port state scanning.
syntax: nmap -p msrpc <target>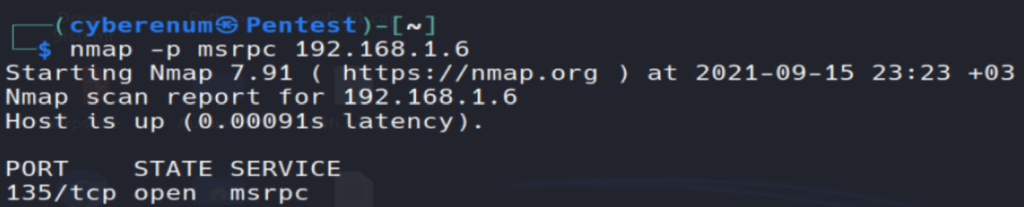
UDP services are mostly ignored during penetration tests, but fine penetration testers know that they often expose host essential information or can even be vulnerable, moreover used to compromise a host. This method demonstrates how to utilize Nmap to list all open UDP ports on a host.
How it Works
UDP scan works by sending a UDP packet to every destination port and analyzing the response to determine the port’s state; it is a connection-less protocol. For some common ports, such as 53 and 161, a protocol-specific payload is sent to increase the response rate, and a service will respond with a UDP packet, proving that it is “open”. If the port is “closed”, an ICMP Port Unreachable message is received from the target. If no response is received after retransmissions, the port is classified as “open|filtered”. This means that the port could be open, or perhaps packet filters are blocking the communication.
syntax: nmap -sU <target>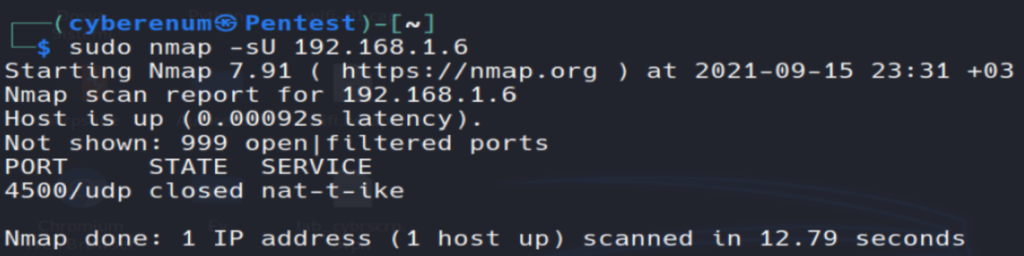
In order to scan a particular UDP port, you can use -p option for port selection nmap -sU -p 4500 192.168.1.6 . Similar to TCP scan we can give a port range and scan all UDP ports nmap -sU -p1-500 192.168.1.6 and nmap -sU -p- 192.168.1.6 .
Apart from the open port enumeration Nmap is quite useful in OS fingerprinting. This scan is very helpful to the penetration tester in order to conclude possible security vulnerabilities and determine the available system calls to set the specific exploit payloads.
syntax: nmap -O <target>Information that is gathered after running the command above:
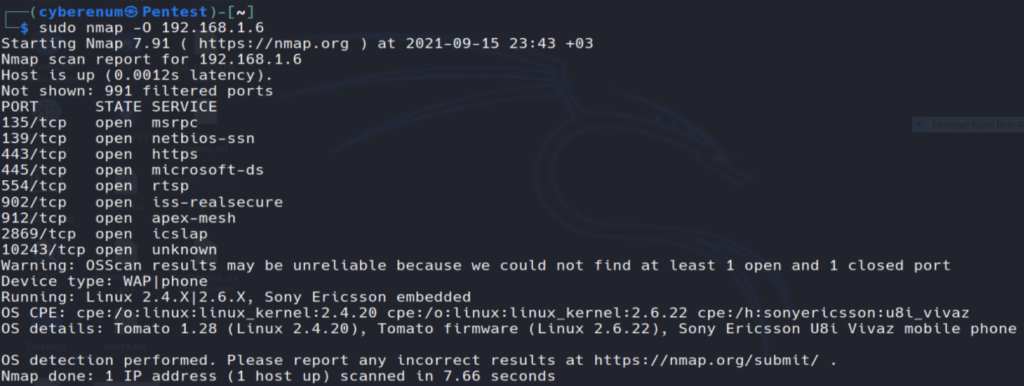
How it Works
The option -O inform Nmap to enable OS detection that identifies a wide variety of systems, including residential routers, IP webcams, operating systems, and many other hardware devices. You can also execute the following command for os detection.
When doing vulnerability assessments of your companies or clients, you really want to know which mail and DNS servers and versions are running. Having an accurate version number helps dramatically in determining which exploits a server is vulnerable to. Version detection helps you obtain this information. Fingerprinting a service may also reveal additional information about a target, such as available modules and specific protocol information. Version scan is also categorized as “Banner Grabbing” in penetration testing.
syntax: nmap -sV <target>
nmap -sV -p135 <target> #specific port version scan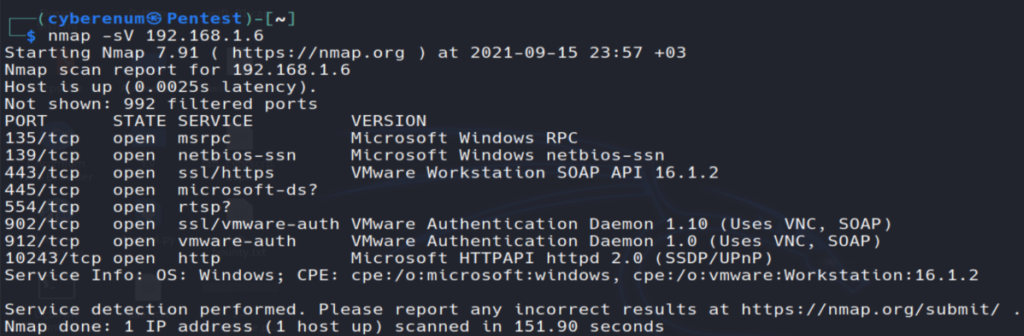
How it Works
The –sV flag informs nmap to works by sending a different query from nmap-service-probes to the list of assumed open ports for banner grabbing. As result it will give output as a table which has an additional column named VERSION, displaying the particular service version. Additional information will be enclosed in parentheses.
IP Protocol scan is quite helpful for determining what communication protocols are being used by a host. This method shows how to use Nmap to enumerate all of the IP protocols, where sends a raw IP packet, without any additional protocol header, to each protocol on the target machine. For the IP protocols TCP, ICMP, UDP, IGMP, and SCTP, Nmap will set valid header values but for the rest, an empty IP packet will be used.
syntax: nmap -sO <target>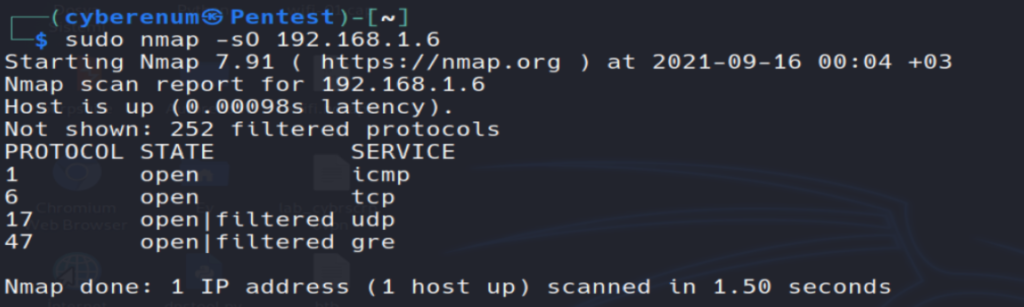
How it Works
The flag -sO tells Nmap to perform an IP Protocol Scan, This kind of scan repeats throughout the protocols found in the file nmap-protocols, and creates IP packets for every entry.
To verify the port state, Nmap categorizes the different responses received as follows:
syntax: nmap -p1,3,5 -sO <target>
nmap -p1-10 -sO <target>The -F option scans only those ports listed in the nmap_services file (or the protocols file if the scan type is -sO). This is far faster than scanning all 65,535 ports. If you will compare scanned time from the above-scanned result, you will notice a time difference between these scans, moreover, it does not show open ports of other running services which the above scan has shown.
syntax: nmap -F <target>The main timing option is set through the -T parameter if you may want more control over the timing in order to get the scan over and done quicker. However, Nmap adjusts its timings automatically depending on the network speed and response times of the victim. Nmap offers six timing templates (T0-5).
syntax: nmap T[option] <target>
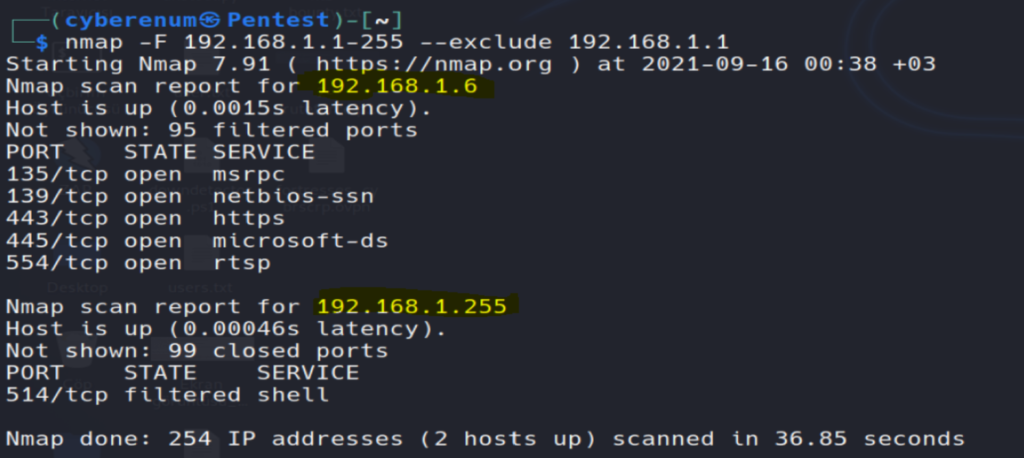
T0: paranoid, T1: sneaky, T2: polite, T3: normal, T4: aggressive, T5: insaneThere will be circumstances where a host exception is required to avoid scanning certain machines. Such as a government website or IP, you may not have the authorization, or might that the host has already been scanned. Nmap option –exclude helps you to eliminate a host or list of hosts from the complete network scan.
syntax: nmap <IP range> --exlude <target IP address>How it Works
The arguments -F –exclude 192.168.1.1 inform Nmap to perform fast scanning for all IPs between 192.168.1.1 and 192.168.1.255 network, excluding the machines with the IPs 192.168.1.1. nmap -sV -O –exlude-file remove.txt 192.168.1.1/24. Excluding a host list from your scans Nmap also supports the argument –exclude-file <filename> in order to exclude the targets listed in <filename>
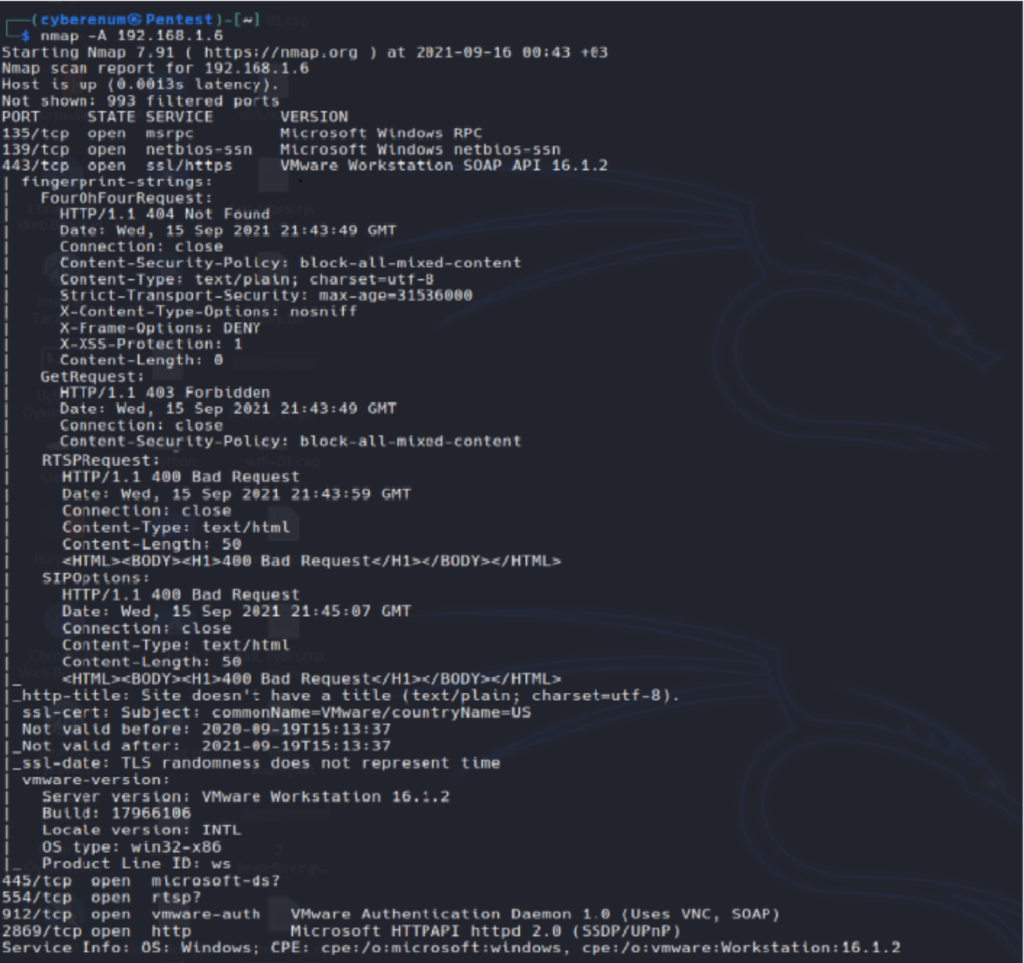
This option enables additional advanced and aggressive options. Presently this enables OS detection (-O), version scanning (-sV), script scanning (-sC), and traceroute (–traceroute). This option only enables features, and not timing options (such as -T4) or verbosity options (-v) that you might want as well. You can see this by using one of the following commands:
syntax: nmap -A <target>How it Works
The argument –A inform nmap to perform an advanced aggressive scan to enumerate versions of running service, OS detection, traceroute of hop and host script scanning of the host machine. Therefore it will take some time in scanning, you can add –T4 timing template to increase the rate of scanning.
When you want to scan multiple hosts to perform more than one scanning then –iL option is used which supports Nmap to load the targets from an external file. You need to add all targeted IP in a text file and save it at a location. To load the targets from the file targets.txt, the following command can be used
syntax: namp -iL ~/target.txtWith a combination of different scan methods, you can improve the effects of nmap. Thank you for reading.
Omer Faruk Kerman